Export decline not tied to global demand, says expert
![]()

Non-oil domestic exports fell 20.7% YoY in March.
11 hours ago
Export decline not tied to global demand, says expert
Non-oil domestic exports fell 20.7% YoY in March.
11 hours ago
Gazelle Ventures offers to acquire No Signboard shares at $0.0021 apiece
The offer will close next month.
1 hour ago
Transition to zero and near-zero-emission fuels could create 700 jobs
This shift will also bring health and economic benefits.
2 hours ago
Food factory at 30 & 32 Tuas Avenue 12 up for sale for $19.0m
JLL is selling the property via private treaty.
3 hours ago
Apple CEO Tim Cook to meet with Singapore leaders: report
His trip follows Apple's US$350m campus expansion announcement in Ang Mo Kio.
4 hours ago
Singapore and Netherlands to establish container tracking service
This is Singapore’s second agreement under the Track and Trace Service.
4 hours ago
Singapore ready to tap Philippine market potential
For years, Singapore has been a top foreign investor in the Philippines.
4 hours ago
CICT NPI rises 6.3% YoY to $293.7M in 1Q24
Gross rental income growth and lower operating expenses drove the uptick.
5 hours ago
MAS issues 8-year prohibition orders to ex-Prudential rep
The former Prudential rep misappropriated $117K in premiums.
5 hours ago
Allianz Partners collaborates with MoneyHero for travel insurance
The policy is underwritten by Tokio Marine Insurance Singapore.
7 hours ago
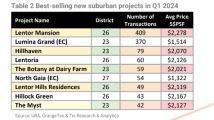
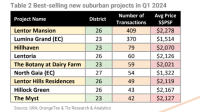
More homes in the suburbs sold at $2m price: OrangeTee
Buyers likely more willing to pay higher prices for their OCR condos.
11 hours ago
Stronger demand push condo and HDB rents higher
“Too early to call bottom.”
11 hours ago
Daily Markets Briefing: STI up 01.08%; Top stock is DBS
DBS is the top stock with a 1.334% increase.
11 hours ago
Private home sales struggle, down 5.3% in first quarter
Year-on-year. Sales dropped 3.1%.
11 hours ago
Singapore Polytechnic launches training facility for food manufacturing
The facility will provide training under the institution’s INC.
1 day ago
CICT NPI rises 6.3% YoY to $293.7M in 1Q24
5 hours ago
Stronger demand push condo and HDB rents higher
11 hours ago
Highlights
Highlights
Partner Content
Partner Content
Exclusives
Exclusives
Financial Services
Industry boosts accounting appeal with new roles, education programmes
There has been a 10% decrease in accounting degree students at universities in Singapore.
2 days ago
Top News
Export decline not tied to global demand, says expert
![]()

Non-oil domestic exports fell 20.7% YoY in March.
11 hours ago
Export decline not tied to global demand, says expert
Non-oil domestic exports fell 20.7% YoY in March.
11 hours ago
Gazelle Ventures offers to acquire No Signboard shares at $0.0021 apiece
The offer will close next month.
1 hour ago
Transition to zero and near-zero-emission fuels could create 700 jobs
This shift will also bring health and economic benefits.
2 hours ago
Food factory at 30 & 32 Tuas Avenue 12 up for sale for $19.0m
JLL is selling the property via private treaty.
3 hours ago
Apple CEO Tim Cook to meet with Singapore leaders: report
His trip follows Apple's US$350m campus expansion announcement in Ang Mo Kio.
4 hours ago
Singapore and Netherlands to establish container tracking service
This is Singapore’s second agreement under the Track and Trace Service.
4 hours ago
Singapore ready to tap Philippine market potential
For years, Singapore has been a top foreign investor in the Philippines.
4 hours ago
CICT NPI rises 6.3% YoY to $293.7M in 1Q24
Gross rental income growth and lower operating expenses drove the uptick.
5 hours ago
MAS issues 8-year prohibition orders to ex-Prudential rep
The former Prudential rep misappropriated $117K in premiums.
5 hours ago
Allianz Partners collaborates with MoneyHero for travel insurance
The policy is underwritten by Tokio Marine Insurance Singapore.
7 hours ago
More homes in the suburbs sold at $2m price: OrangeTee
Buyers likely more willing to pay higher prices for their OCR condos.
11 hours ago
Stronger demand push condo and HDB rents higher
“Too early to call bottom.”
11 hours ago
Daily Markets Briefing: STI up 01.08%; Top stock is DBS
DBS is the top stock with a 1.334% increase.
11 hours ago
Private home sales struggle, down 5.3% in first quarter
Year-on-year. Sales dropped 3.1%.
11 hours ago
Singapore Polytechnic launches training facility for food manufacturing
The facility will provide training under the institution’s INC.
1 day ago
CICT NPI rises 6.3% YoY to $293.7M in 1Q24
5 hours ago
Stronger demand push condo and HDB rents higher
11 hours ago
Partner Content
Partner Content
Highlights
Highlights
Exclusives
Financial Services
Industry boosts accounting appeal with new roles, education programmes
There has been a 10% decrease in accounting degree students at universities in Singapore.
2 days ago
Event News
Event News
NTUC LearningHub Pte Ltd wins Digital - Training and Development Award at SBR Technology Excellence Awards 2024
Co-Written / Partner
It was honoured for its significant contribution towards enhancing Singapore's tech workforce readiness.
Co-Written / Partner
NTUC LearningHub Pte Ltd wins Digital - Training and Development Award at SBR Technology Excellence Awards 2024
It was honoured for its significant contribution towards enhancing Singapore's tech workforce readiness.




































































 Advertise
Advertise






























Commentary
AI is revolutionising learning: Why should educational institutions in Singapore embrace this change?
Seeking an office space in Singapore: Where do you start?